What is Coos Ransomware Coos Ransomware is another crypto-virus that is one of the most dangerous threats to user data. Like many similar threats, Coos
Category: Ransomware
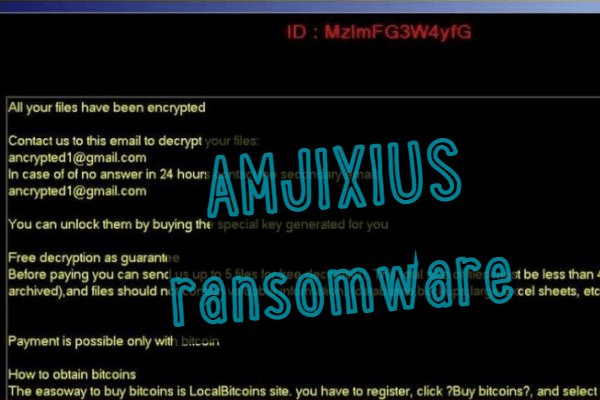
How to remove AMJIXIUS Ransomware and decrypt .amjixius files
What is AMJIXIUS Ransomware Lately, the cryptovirus has become the most active, namely in late December. AMJIXIUS is a cryptovirus that encrypts user data, such
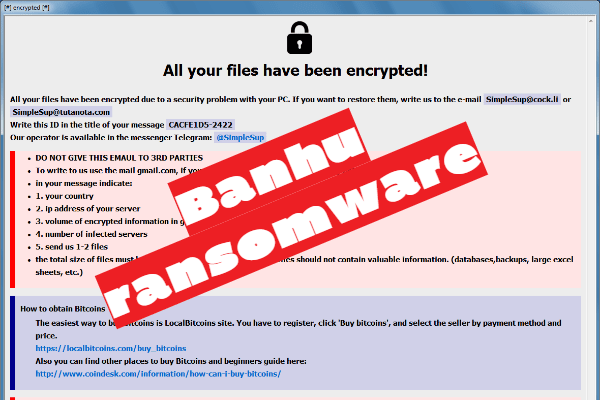
How to remove Banhu Ransomware and decrypt .banhu files
What is Banhu Ransomware Banhu (板胡, pinyin: bǎnhú – is a Chinese traditional bowed string instrument in the huqin family of instruments) – it is
How to remove Igal Ransomware and decrypt .igal files
What is Igal Ransomware Igal Ransomware is another product of cybercriminals who have written a large family of crypto viruses known as STOP (DjVu). Like
How to remove Povlsomware Ransomware and decrypt .povlsomware files
What is Povlsomware Ransomware Povlsomware (alternative name is RansomeToad) – it is a cryptographer extortionists. This cryptovirus encrypts user files of various formats, including video,
How to remove Mijnal Ransomware and decrypt .mijnal files
What is Mijnal Ransomware Recently, more and more new and new crypto viruses appear. Mijnal Ransomware is one of them. Like other analogs, it encrypts
How to remove Ziggy Ransomware and decrypt .ziggy files
What is Ziggy Ransomware Ziggy is a regular сryptovirus that encrypts user data of various formats and directivity. Like analogs, Ziggy uses a special AES+RSA
How to remove Uh-Oh Ransomware and decrypt .jgy files
What is Uh-Oh Ransomware Uh-Oh ransomware is a cryptovirus that became most active in December of this year. This is a cryptovirus that builds user
How to remove JCrypt Ransomware and decrypt .jcrypt files
What is JCrypt Ransomware JCrypt is a new cryptovirus that can cause a lot of trouble. The virus encrypts user files, after which they become
How to remove BlueEagle Ransomware and decrypt ..maxsteel.saher blue eagle
What is BlueEagle Ransomware BlueEagle is a fairly common cryptovirus, which can be called Saher Blue Eagle. This encrypts user files, including archives, audio, video,