xDec Ransomware is a type of malicious software that infects computers by encrypting the files on the system and then demanding a ransom in exchange for the decryption key. It typically spreads through email attachments, malicious websites, or vulnerabilities in software.
Once infected, xDec Ransomware adds a specific file extension to the encrypted files, such as “.xdec“. It uses a strong encryption algorithm to lock the files, making them inaccessible without the decryption key.
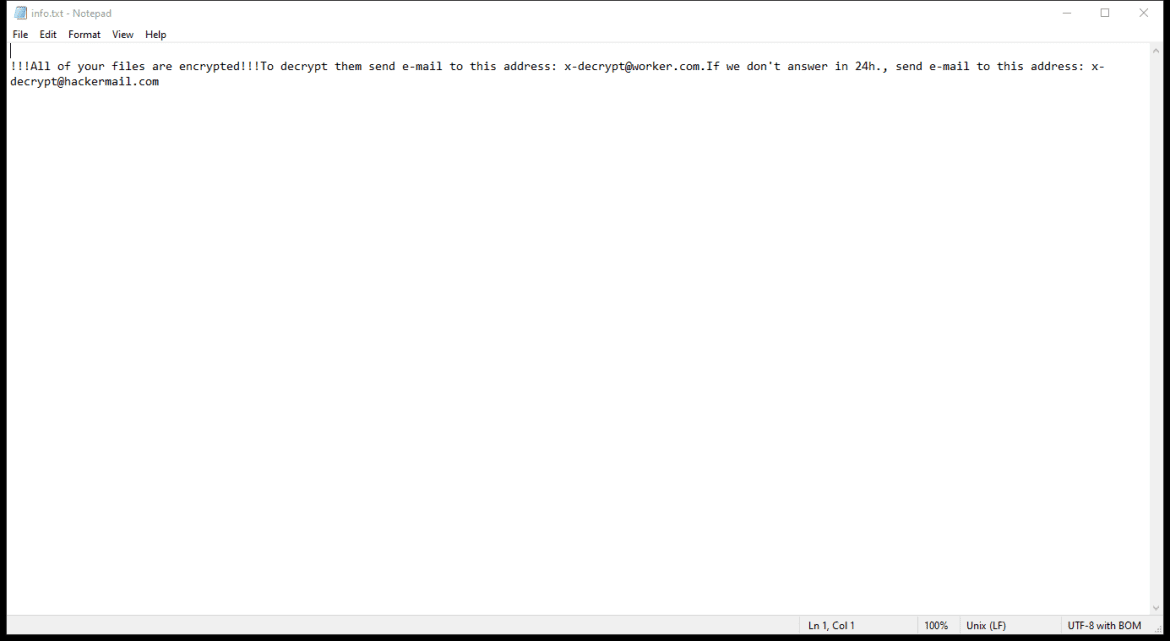
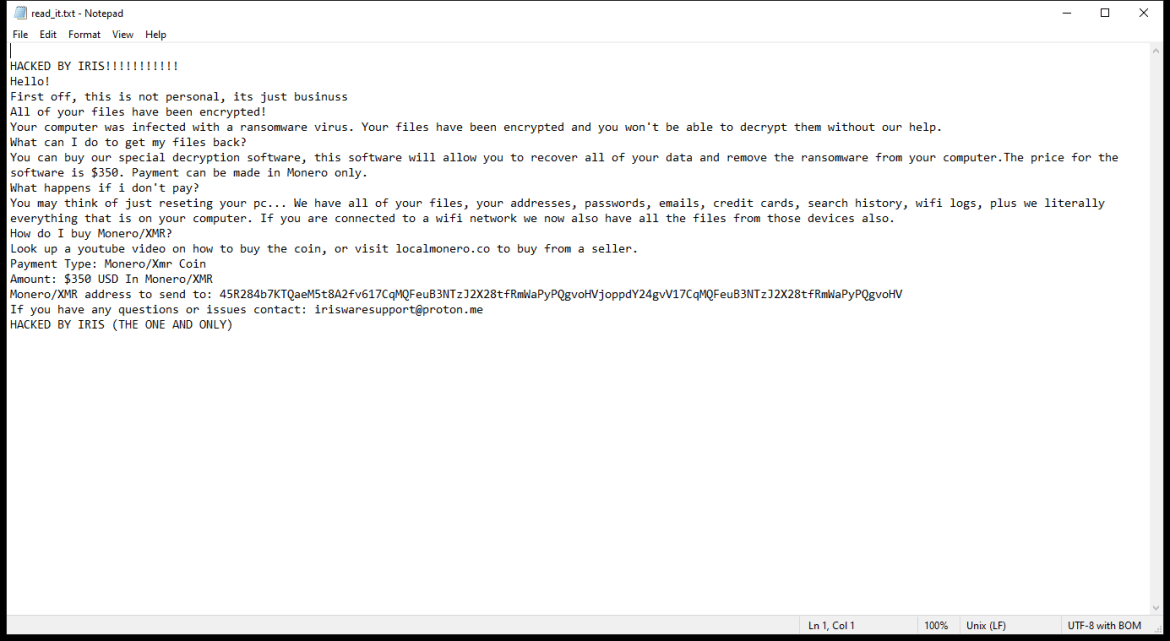
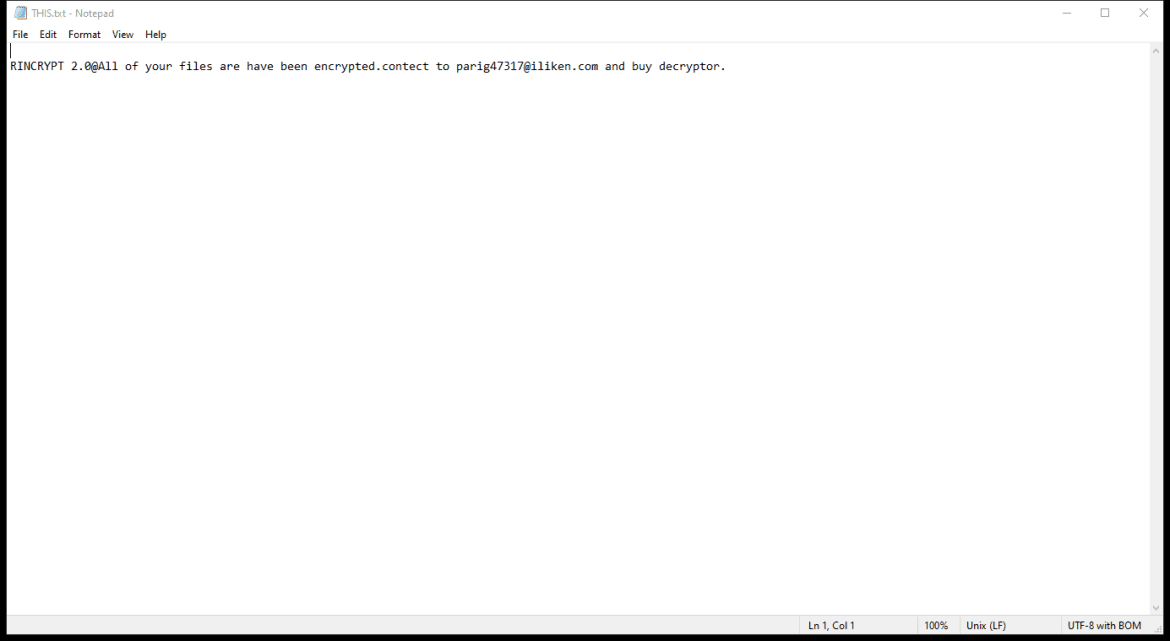
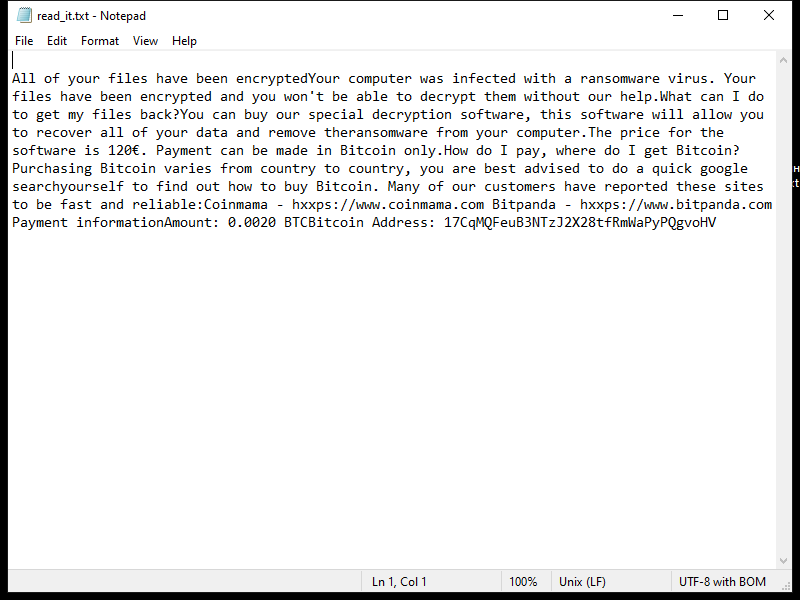
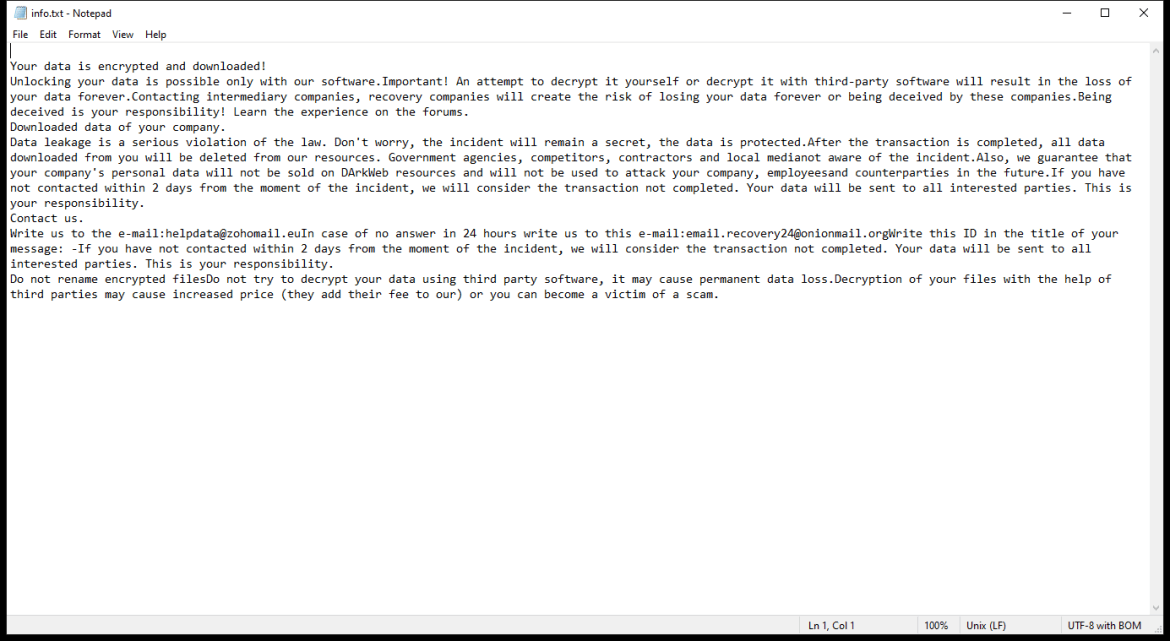
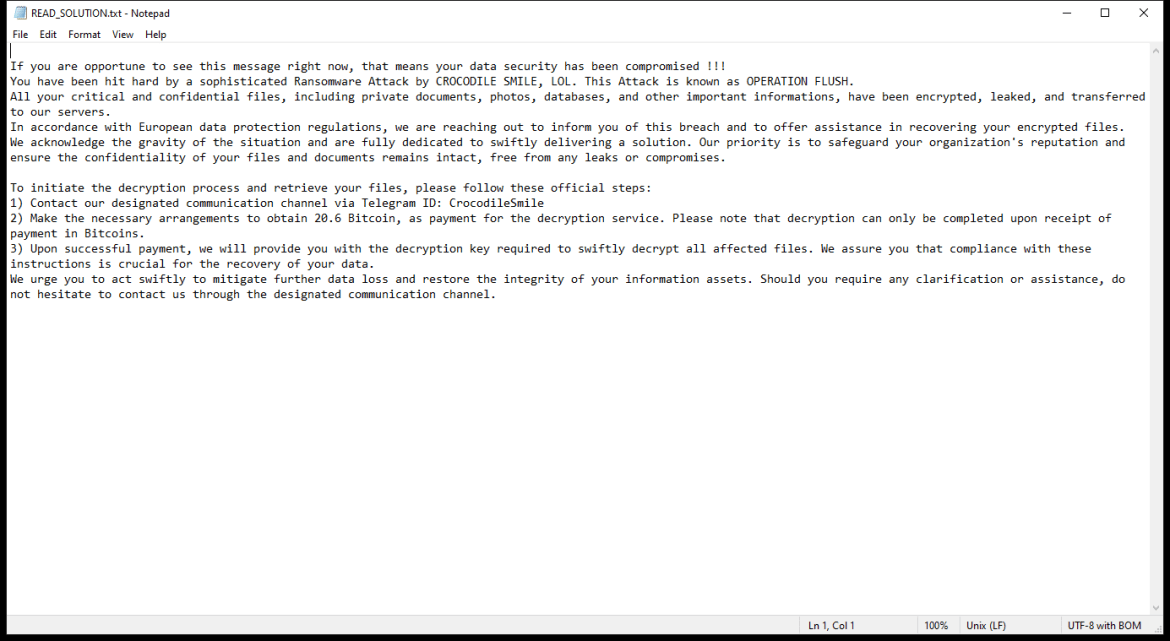
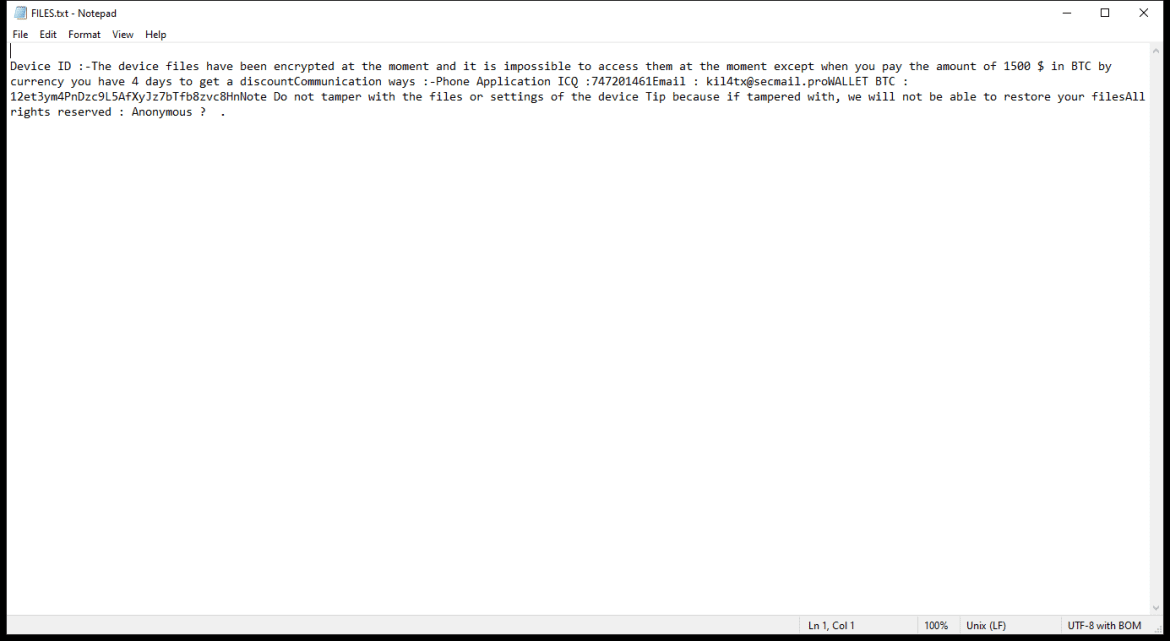
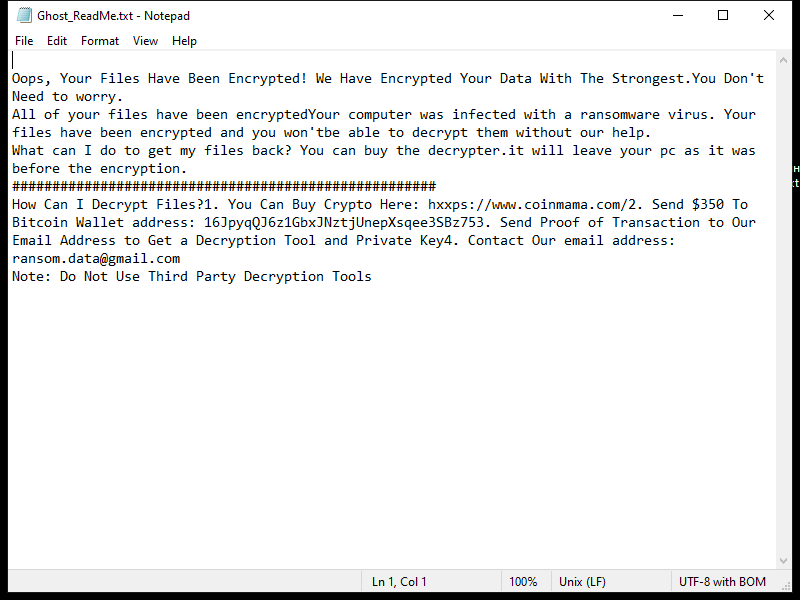
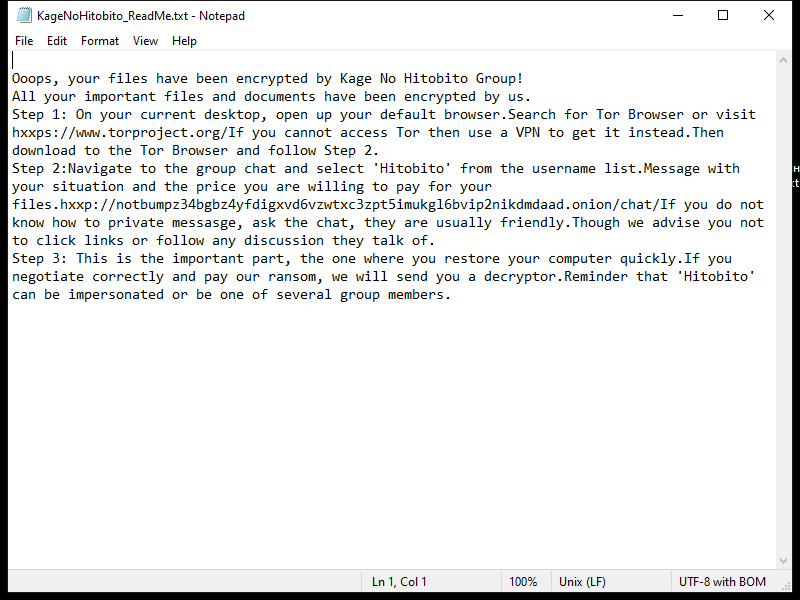
The ransomware creates a ransom note containing instructions on how to pay the ransom and obtain the decryption key. This note is usually placed on the desktop or in folders containing encrypted files.
As of now, there are no known decryption tools available for xDec Ransomware. However, it is recommended not to pay the ransom as there is no guarantee that the cybercriminals will provide the decryption key or that it will work properly.
If your files have been encrypted by xDec Ransomware, you may try to restore them from a backup or use file recovery software to recover the original, unencrypted versions. It is also advisable to seek assistance from cybersecurity professionals or law enforcement agencies for further guidance on how to handle the situation.