What is MountLocket Ransomware
MountLocket Ransomware (Cbtucyny) is an encryption virus that encrypts user data using the AES+RSA algorithm. Speaking of actions, we note that MountLocket Ransomware is no different from a number of other ransomware. The cryptovirus encrypts files of MountLocketous formats, which leads to their complete inoperability. This virus was spotted in mid-August 2020, in just a few MountLocket Ransomware days around the world, and is extorting money from users around the world. Although, of course, scammers initially target large companies and corporations. You will find an explanation for this below. Also, MountLocket Ransomware changes the extensions of encrypted files to the pattern .ReadManual.
No genealogical relationship has been identified at the moment. Initially, MountLocket Ransomware is aimed at English-speaking users, however, according to our information, this “infection” has spread almost all over the world. Like many other viruses, MountLocket Ransomware creates a file called RecoveryManual.html containing the cybercriminals’ demands. So, special attention is drawn to the fact that cybercriminals are demanding a ransom in the amount of two million dollars in the form of cryptocurrency. Agree, ordinary users cannot afford this, and large organizations prefer not to advertise such cases of cyber attacks. This is what the requirements note looks like:
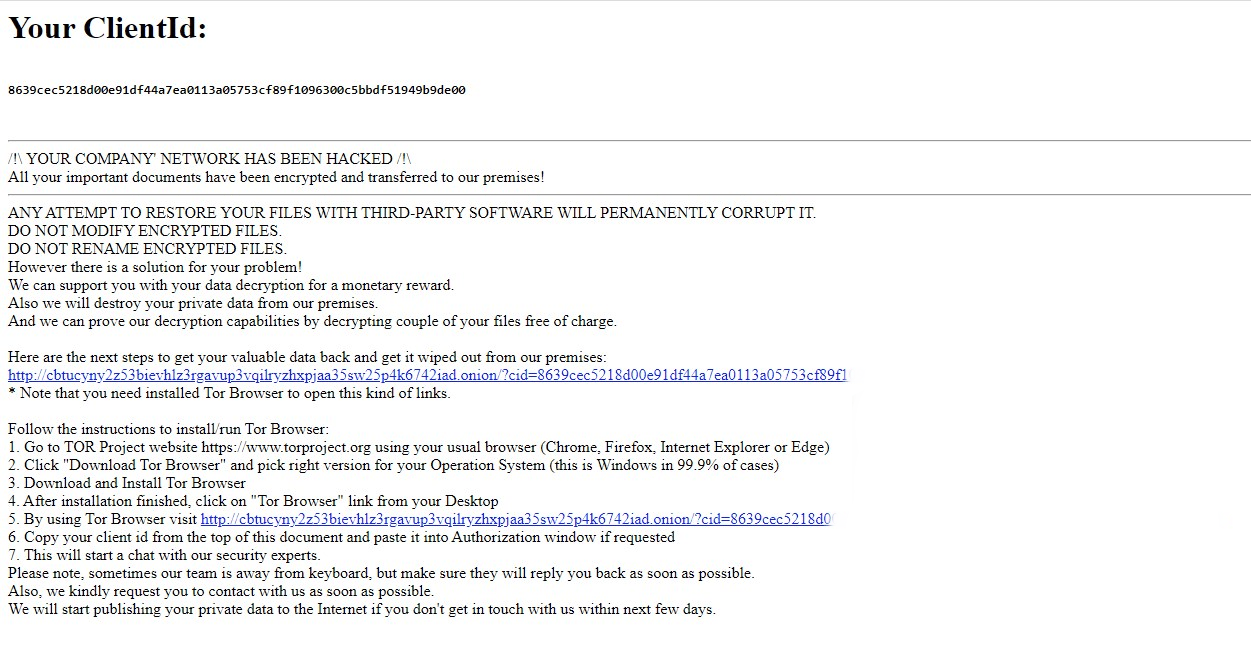
Your ClientId:
8639cec5218d00e91df44a7ea0113a05753cf89*************************
/!\ YOUR COMPANY’ NETWORK HAS BEEN HACKED /!\
All your important documents have been encrypted and transferred to our premises!
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.
However there is a solution for your problem!
We can support you with your data decryption for a monetary reward.
Also we will destroy your private data from our premises.
And we can prove our decryption capabilities by decrypting couple of your files free of charge.
Here are the next steps to get your valuable data back and get it wiped out from our premises:
http://cbtucyny2z53bievhlz3rgavup3vqilryzhxpjaa35sw25p4k6742iad.onion/?cid=8639cec5218d00e91df44a7ea0113a05753cf89*************************
* Note that you need installed Tor Browser to open this kind of links.
Follow the instructions to install/run Tor Browser:
1. Go to TOR Project website https://www.torproject.org using your usual browser (Chrome, Firefox, Internet Explorer or Edge)
2. Click “Download Tor Browser” and pick right version for your Operation System (this is Windows in 99.9% of cases)
3. Download and Install Tor Browser
4. After installation finished, click on “Tor Browser” link from your Desktop
5. By using Tor Browser visit http://cbtucyny2z53bievhlz3rgavup3vqilryzhxpjaa35sw25p4k6742iad.onion/?cid=8639cec5218d00e91df44a7ea0113a05753cf89*************************
6. Copy your client id from the top of this document and paste it into Authorization window if requested
7. This will start a chat with our security experts.
Please note, sometimes our team is away from keyboard, but make sure they will reply you back as soon as possible.
Also, we kindly request you to contact with us as soon as possible.
We will start publishing your private data to the Internet if you don’t get in touch with us within next few days.
Here is an example of communicating with scammers:
Fraudsters try to intimidate the victim by giving them a limited time limit to pay the ransom. Moreover, cybercriminals threaten to disclose private data on their website, which may be of some help for competitors, but the website does not exist as such. If you are an ordinary user who does not have $ 2 million, or you are a representative of a large company, but your plans do not include telling your boss about this problem, you can use our recommendations to remove MountLocket Ransomware and decrypt .ReadManual.
Well, there are 2 options for solving this problem. The first is to use an automatic removal utility that will remove the threat and all instances related to it. Moreover, it will save you time. Or you can use the Manual Removal Guide, but you should know that it might be very difficult to remove MountLocket ransomware manually without a specialist’s help.
If for any reason you need to recover deleted or lost files, then check out our article Top 5 Deleted File Recovery Software
MountLocket Removal Guide

Remember that you need to remove MountLocket Ransomware first and foremost to prevent further encryption of your files before the state of your data becomes totally useless. And only after that, you can start recovering your files. Removal must be performed according to the following steps:
- Download MountLocket Removal Tool.
- Remove MountLocket from Windows (7, 8, 8.1, Vista, XP, 10) or Mac OS (Run system in Safe Mode).
- Restore .MountLocket files
- How to protect PC from future infections.
How to remove MountLocket ransomware automatically:
Norton is a powerful antivirus that protects you against malware, spyware, ransomware and other types of Internet threats. Norton is available for Windows, macOS, iOS and Android devices. We recommend you to try it.
If you’re Mac user – use this.
Manual MountLocket Removal Guide
Here are step-by-step instructions to remove MountLocket from Windows and Mac computers. Follow these steps carefully and remove files and folders belonging to MountLocket. First of all, you need to run the system in a Safe Mode. Then find and remove needed files and folders.
Uninstall MountLocket from Windows or Mac
Here you may find the list of confirmed related to the ransomware files and registry keys. You should delete them in order to remove virus, however it would be easier to do it with our automatic removal tool. The list:
MountLocket.dll
_readme.txt
readme.txt
Windows 7/Vista:
- Restart the computer;
- Press Settings button;
- Choose Safe Mode;
- Find programs or files potentially related to MountLocket by using Removal Tool;
- Delete found files;
Windows 8/8.1:
- Restart the computer;
- Press Settings button;
- Choose Safe Mode;
- Find programs or files potentially related to MountLocket by using Removal Tool;
- Delete found files;
Windows 10:
- Restart the computer;
- Press Settings button;
- Choose Safe Mode;
- Find programs or files potentially related to MountLocket by using Removal Tool;
- Delete found files;
Windows XP:
- Restart the computer;
- Press Settings button;
- Choose Safe Mode;
- Find programs or files potentially related to MountLocket by using Removal Tool;
- Delete found files;
Mac OS:
- Restart the computer;
- Press and Hold Shift button, before system will be loaded;
- Release Shift button, when Apple MountLocketo appears;
- Find programs or files potentially related to MountLocket by using Removal Tool;
- Delete found files;
How to restore encrypted files
You can try to restore your files with special tools. You may find more detailed info on data recovery software in this article – recovery software. These programs may help you to restore files that were infected and encrypted by ransomware.
Restore data with Stellar Data Recovery
Stellar Data Recovery is able to find and restore different types of encrypted files, including removed emails.
- Download and install Stellar Data Recovery
- Choose drives and folders with your data, then press Scan.
- Select all the files in a folder, then click on Restore button.
- Manage export location. That’s it!
Restore encrypted files using Recuva
There is an alternative program, that may help you to recover files – Recuva.
- Run the Recuva;
- Follow instructions and wait until scan process ends;
- Find needed files, MountLocket them and Press Recover button;
How to prevent ransomware infection?
It is always rewarding to prevent ransomware infection because of the consequences it may bring. There are a lot of difficulties in resolving issues with encoders viruses, that’s why it is very vital to keep a proper and reliable anti-ransomware software on your computer. In case you don’t have any, here you may find some of the best offers in order to protect your PC from disastrous viruses.
Malwarebytes
SpyHunter is a reliable antimalware removal tool application, that is able to protect your PC and prevent the infection from the start. The program is designed to be user-friendly and multi-functional.
