MIRROR Ransomware is a type of malicious software that encrypts files on an infected computer and demands a ransom from the victim in exchange for the decryption key. Here is some information about MIRROR Ransomware:
1. Infection: MIRROR Ransomware typically infects computers through various methods, including malicious email attachments, fake software updates, or exploit kits that target vulnerabilities in software or operating systems.
2. File Extensions: MIRROR Ransomware usually adds the “.mr” extension to the encrypted files. For example, a file named “document.docx” will be renamed to “document.docx.mr” after encryption.
3. File Encryption: MIRROR Ransomware employs strong encryption algorithms, such as AES or RSA, to lock the victim’s files. These encryption methods ensure that the files cannot be accessed without the decryption key, which the attackers hold.
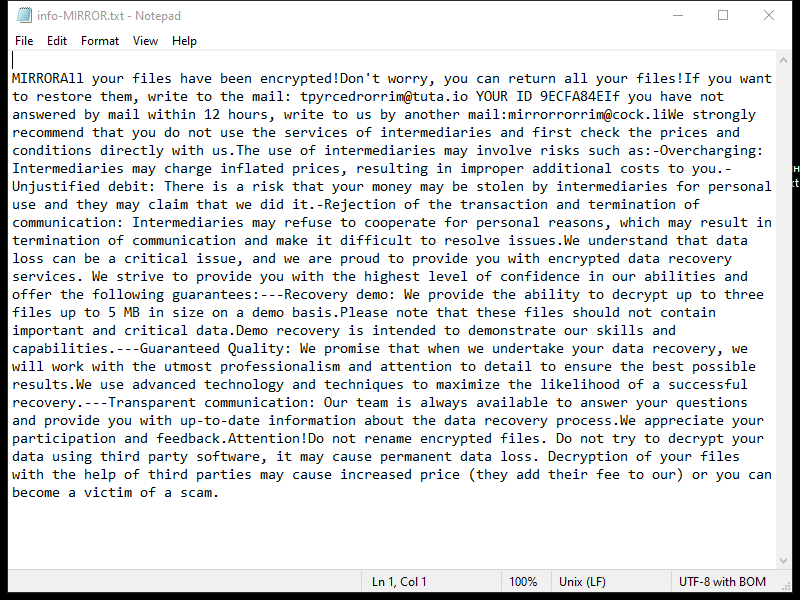
4. Ransom Note: MIRROR Ransomware creates a ransom note typically named “README.txt” or “HOW_TO_DECRYPT.txt” in the infected directories or on the desktop. The note contains instructions on how to pay the ransom and obtain the decryption key.
5. Decryption Tools: At the time of writing, there are no known decryption tools available for MIRROR Ransomware. It is always recommended to avoid paying the ransom as it does not guarantee that the attackers will provide the decryption key or that they won’t target you again in the future.
6. Decrypting .mr Files: Without a decryption tool, decrypting .mr files can be challenging. However, some potential methods to try include:
– Restoring files from a backup: If you have a recent backup of your files, you can restore them after removing the ransomware from your system.
– Seeking professional help: In some cases, cybersecurity experts or specialized organizations may be able to assist in decrypting files affected by certain ransomware strains. However, this is not guaranteed and may vary depending on the specific circumstances.
Remember, prevention is key. To protect yourself from ransomware attacks:
– Keep your operating system and software up to date.
– Be cautious when opening email attachments or clicking on suspicious links.
– Use reputable antivirus software and regularly scan your system.
– Backup your important files regularly and store them in a secure location.