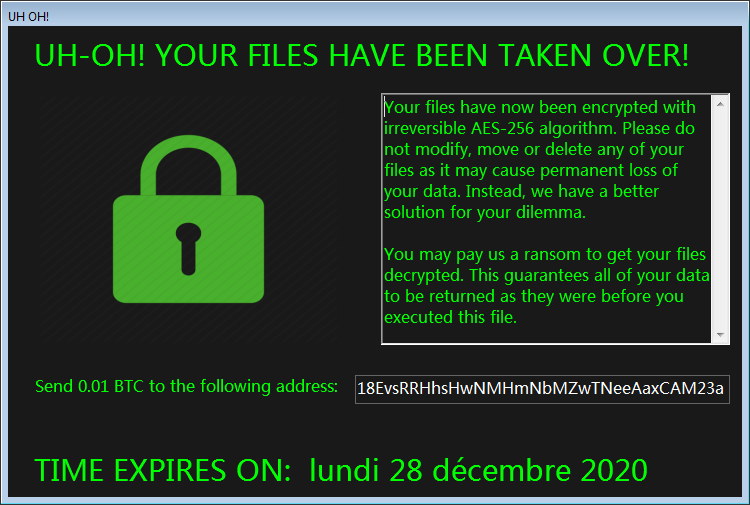
What is cuteRansomware Ransomware cuteRansomware is a cryptovirus, which belongs to the unknown ransomware family. And so, this is a cryptovirus that shuffles user files
Category: Ransomware
How to remove BlackMamba Ransomware and decrypt your files
What is BlackMamba Ransomware BlackMamba is a crypto-virus encrypting user’s files using the AES algorithm. Like analogs, it encrypts office documents, photos, archives, audio, and
How to remove Mifr Ransomware and decrypt .mifr files
What is Mifr Ransomware Mifr ransomware is a cryptovirus that became popular in the middle of December 2020. Initially, the virus is aimed at English-speaking
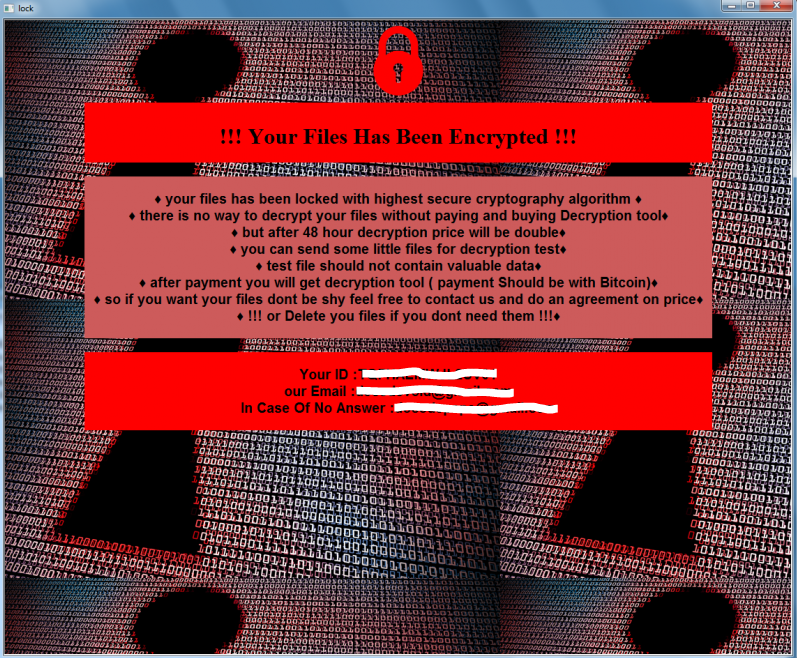
How to remove Thanos Ransomware and decrypt .locked files
What is Thanos Ransomware Thanos is a cryptovirus that encrypts user data with an AES algorithm. This cryptovirus has become very common around the world
How to remove Kobos Ransomware and decrypt .kobos files
What is Kobos Ransomware Kobos (from the Crysis family) has become common in a bad sense of the word. This has spread across the globe
How to remove Legend Ransomware and decrypt .legend files
What is Legend Ransomware Legend is a ransomware, which, like many similar viruses, encrypts user data in various formats. This can be photos, videos, multimedia,
How to remove MONETA Ransomware and decrypt .moneta files
What is MONETA Ransomware MONETA is a cryptovirus from the Phobos family which became popular in the last weeks of December of this year. This
How to remove Leitkcad Ransomware and decrypt .leitkcad files
What is Leitkcad Ransomware In this article, we will talk in detail about Leitkcad Ransomware from the Prometey family that comes to the computer without
How to remove Infection Ransomware and decrypt .infection files
What is Infection Ransomware Infection ransomware is a cryptovirus from NEFILIM family that has become very common in the last week. This virus, like many
How to remove Booa Ransomware and decrypt .booa files
What is Booa Ransomware Booa Ransomware is another crypto-virus from the large Stop (DjVu) family. Aside from the genealogical relationship, it’s worth noting that Booa