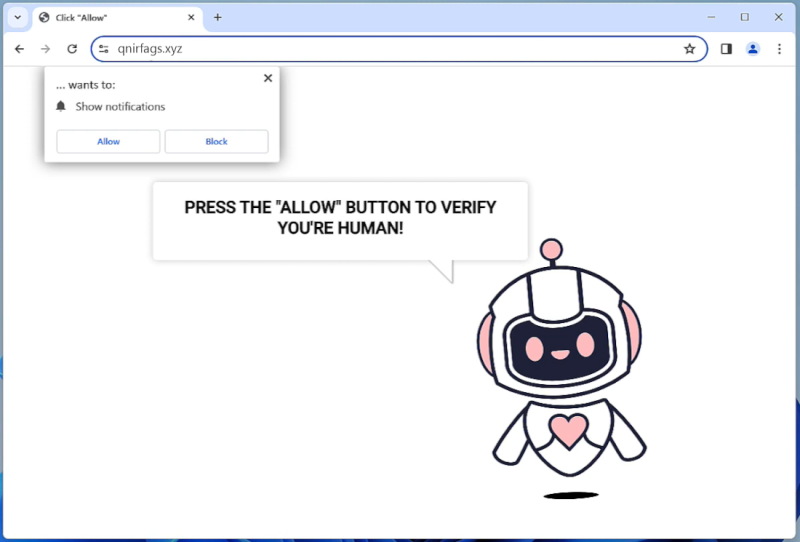
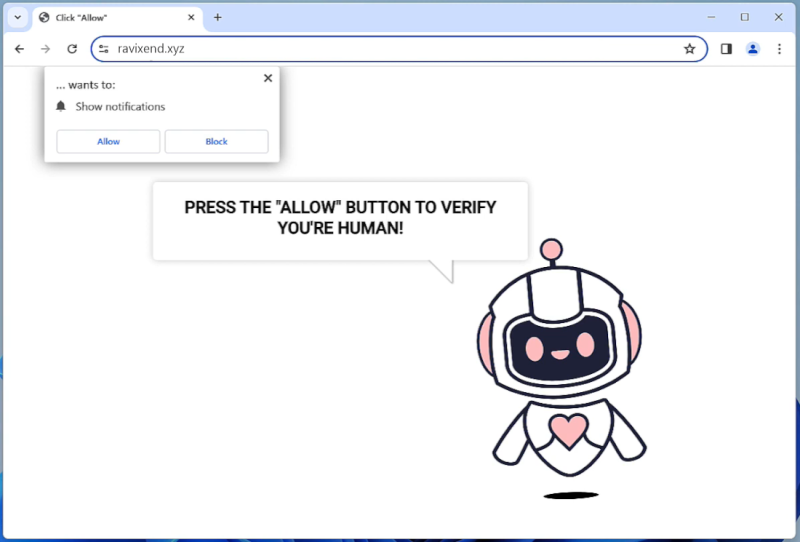
How to remove Qnirfags.xyz
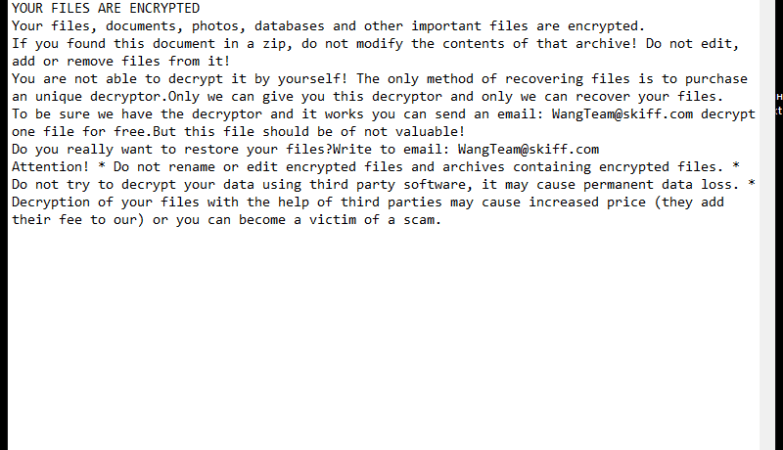
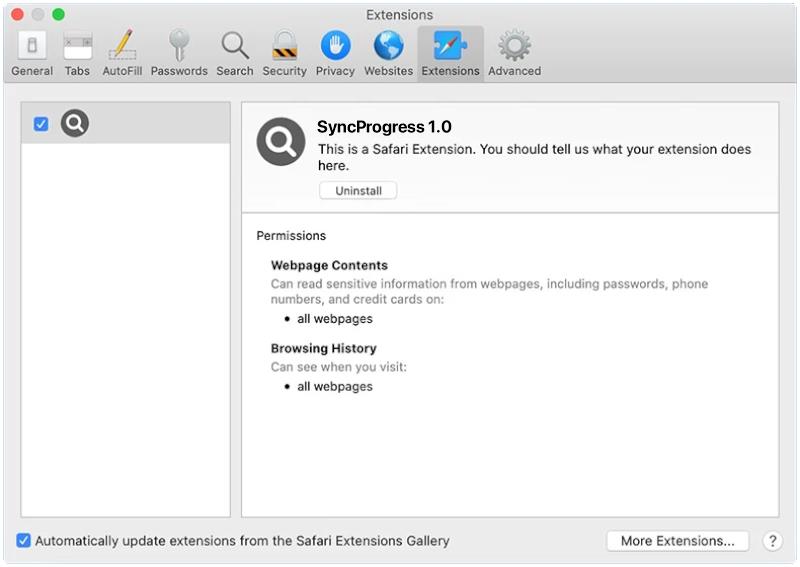
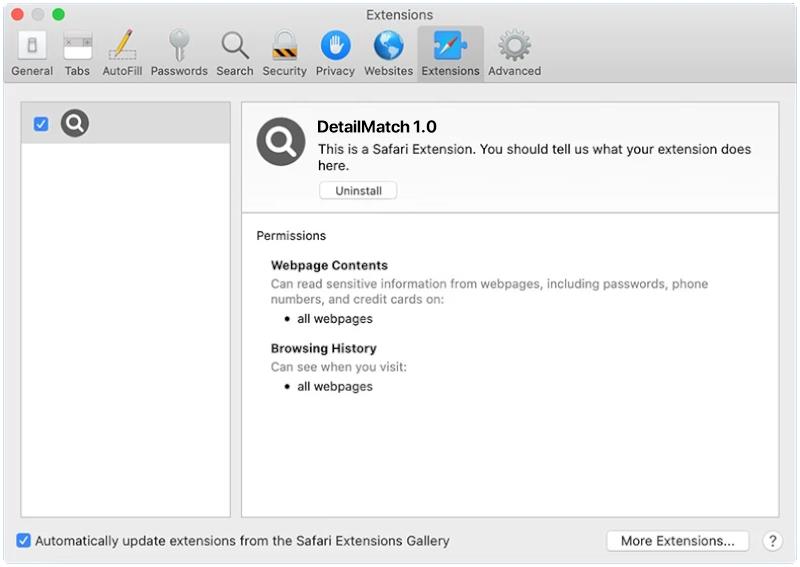
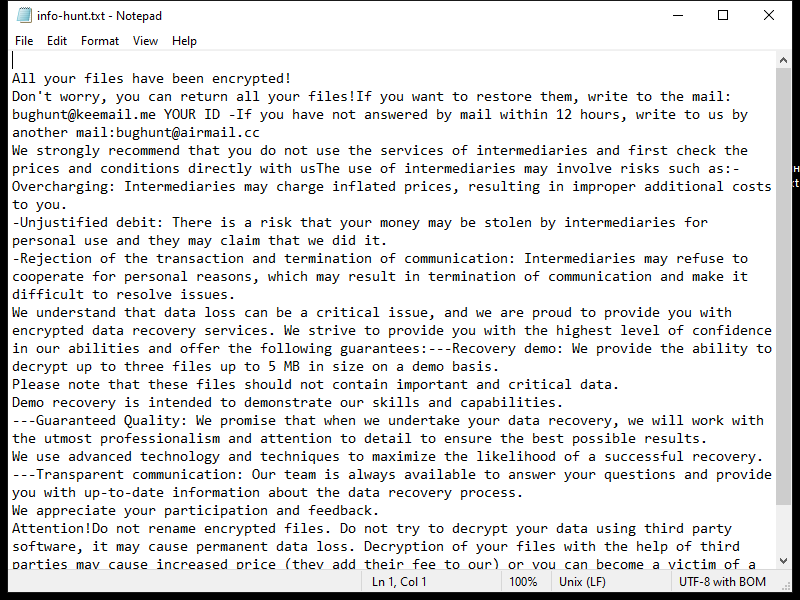
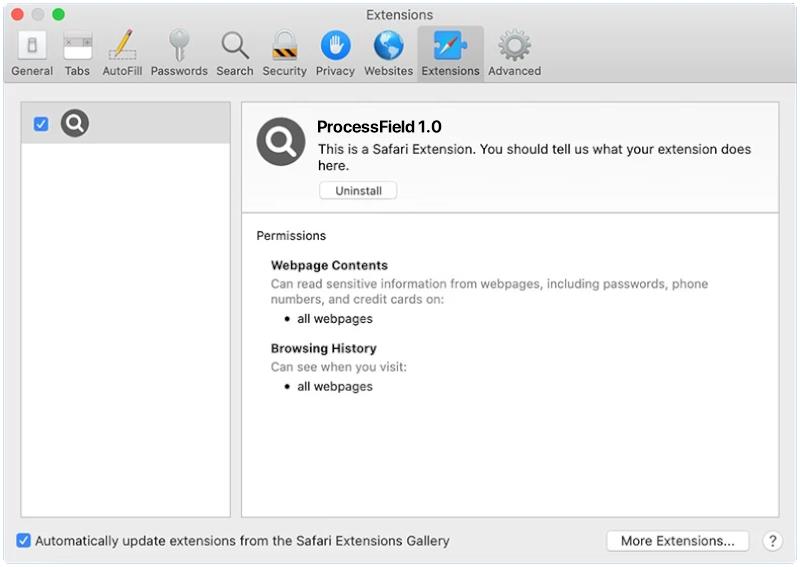
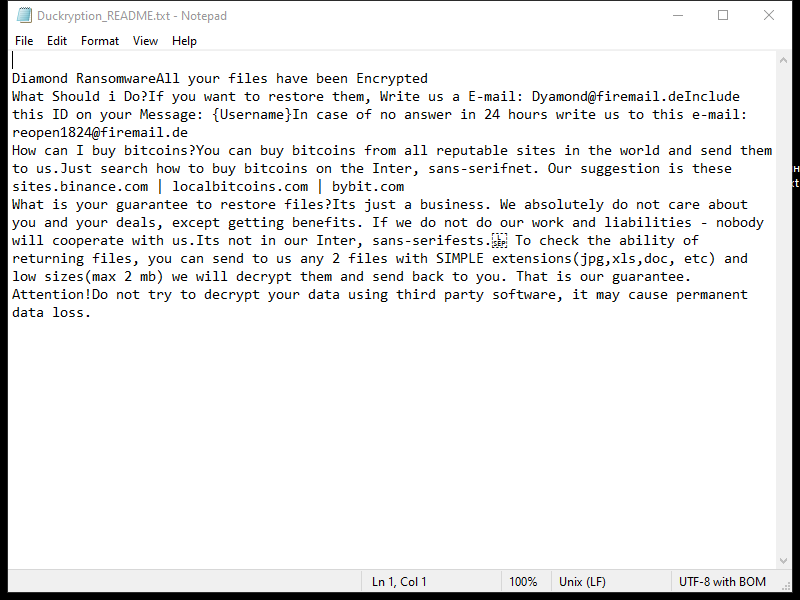
Qnirfags.xyz is a malicious website that is known for infecting computers through various methods such as fake software updates, malicious email attachments, or by tricking users into clicking on deceptive links. Once a computer is infected with Qnirfags.xyz, it can start displaying unwanted pop-up notifications that can be difficult to get rid of.
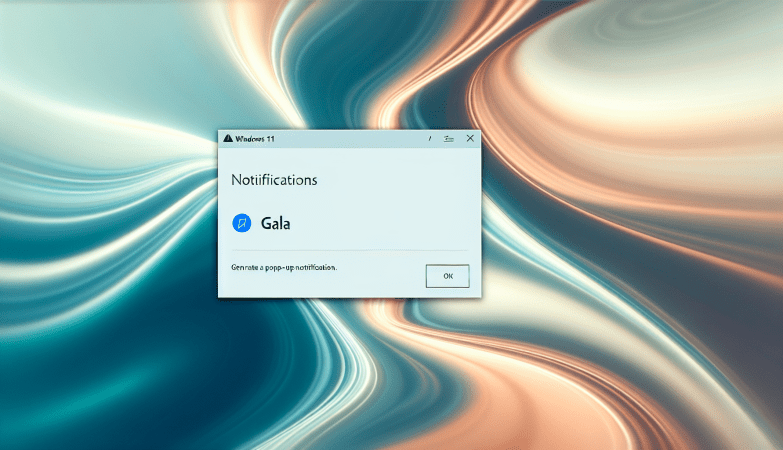
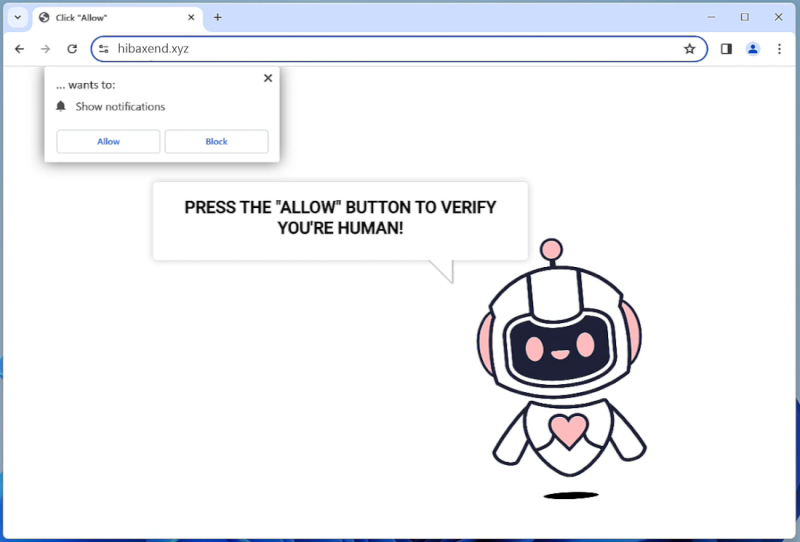
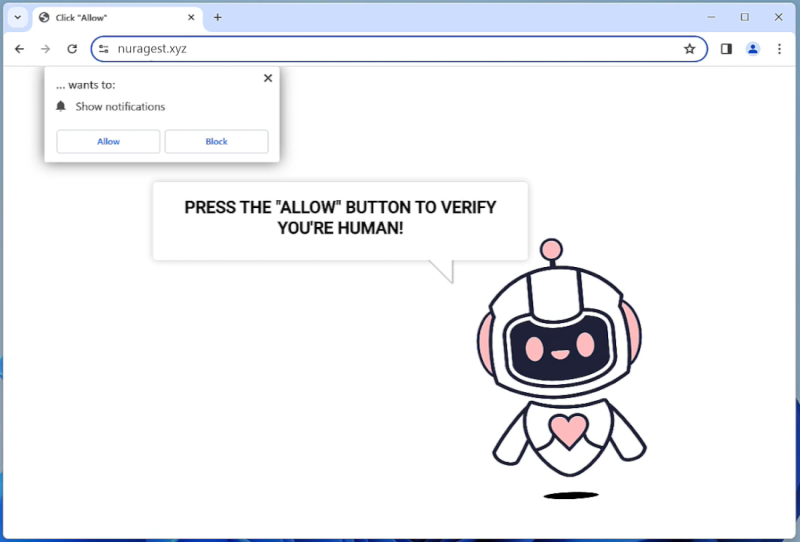
The website exploits browser notifications by prompting users to allow notifications in order to access certain content or services. Once the notifications are enabled, users will start receiving a barrage of spam notifications that can be intrusive and annoying. Qnirfags.xyz can infect a wide range of browsers including Google Chrome, Mozilla Firefox, and Safari, and can affect various devices such as desktop computers, laptops, and mobile devices. It is important for users to be cautious when browsing online and to avoid clicking on suspicious links or downloading unknown software to prevent infections from malicious websites like Qnirfags.xyz.