Capibara Ransomware is a type of ransomware that infects computers by encrypting files and demanding payment for decryption. It typically spreads through malicious email attachments, infected software downloads, or exploiting vulnerabilities in outdated software.
Once infected, Capibara Ransomware adds a specific file extension to encrypted files, such as .capibara. It uses a strong encryption algorithm to lock files, making them inaccessible without the decryption key.
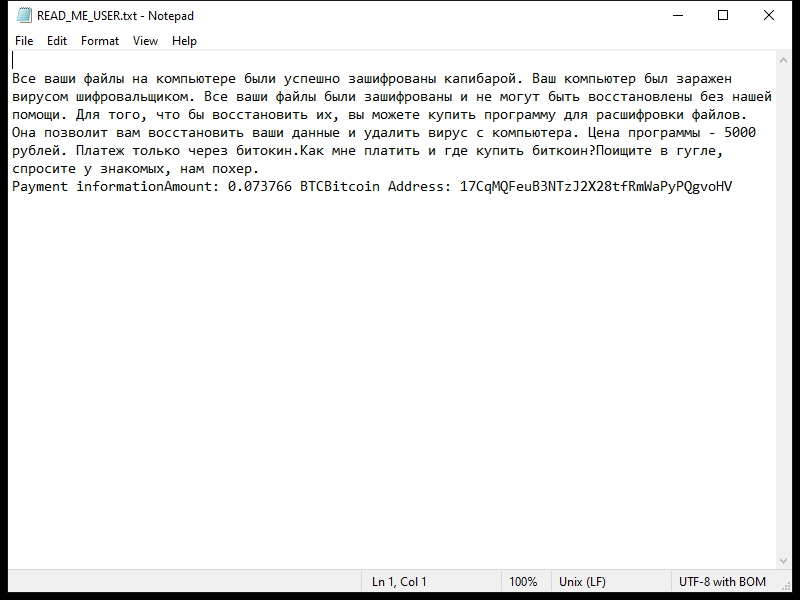
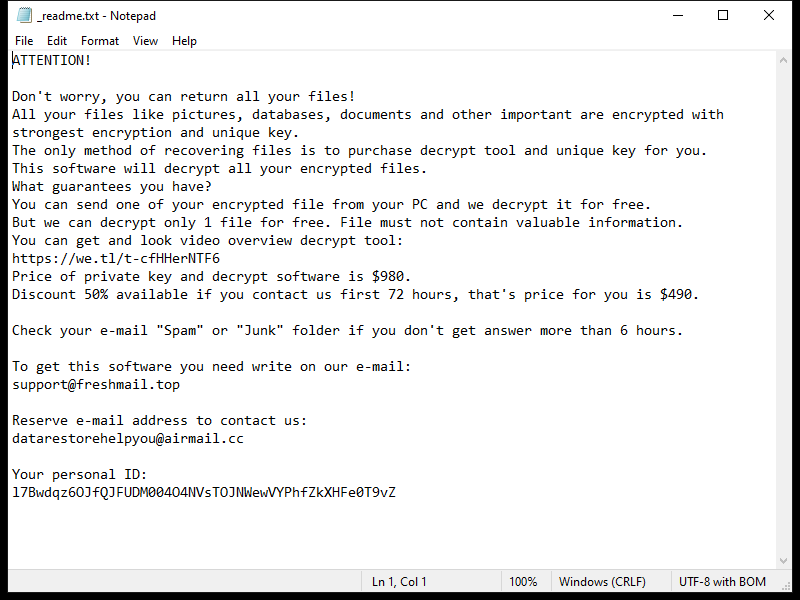
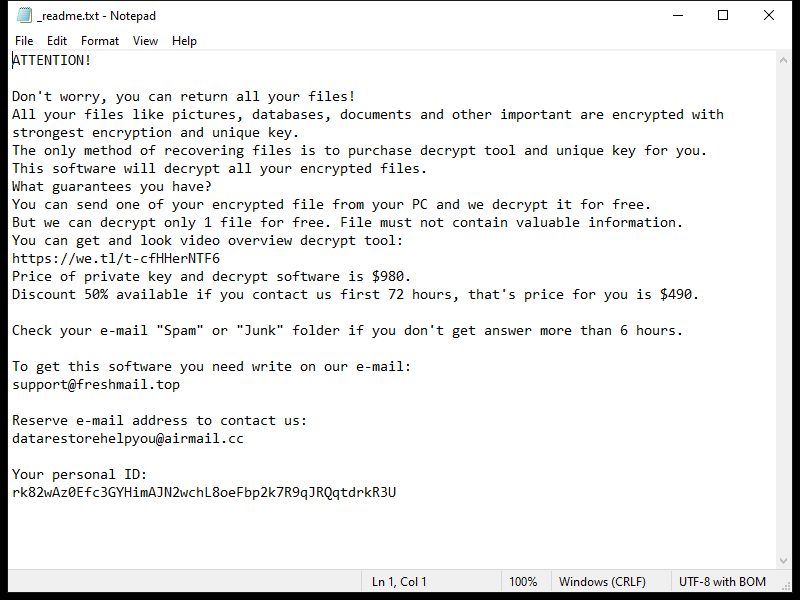
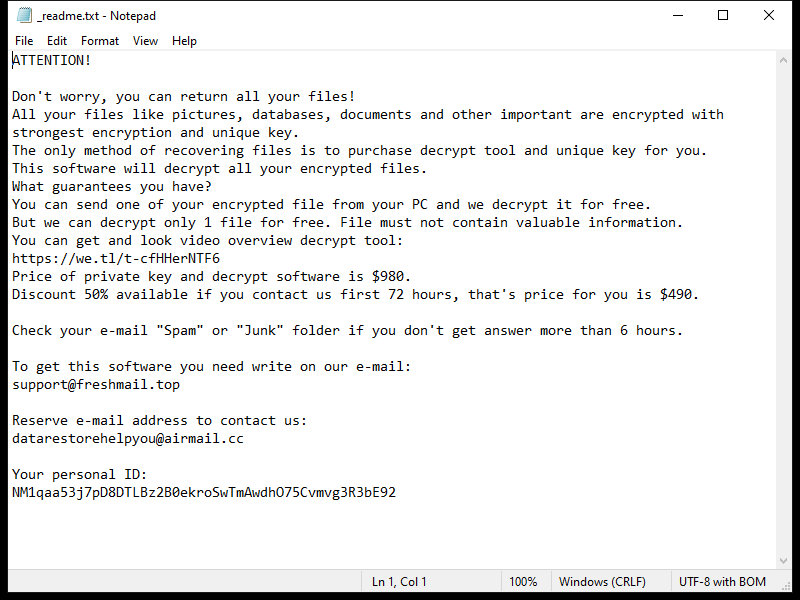
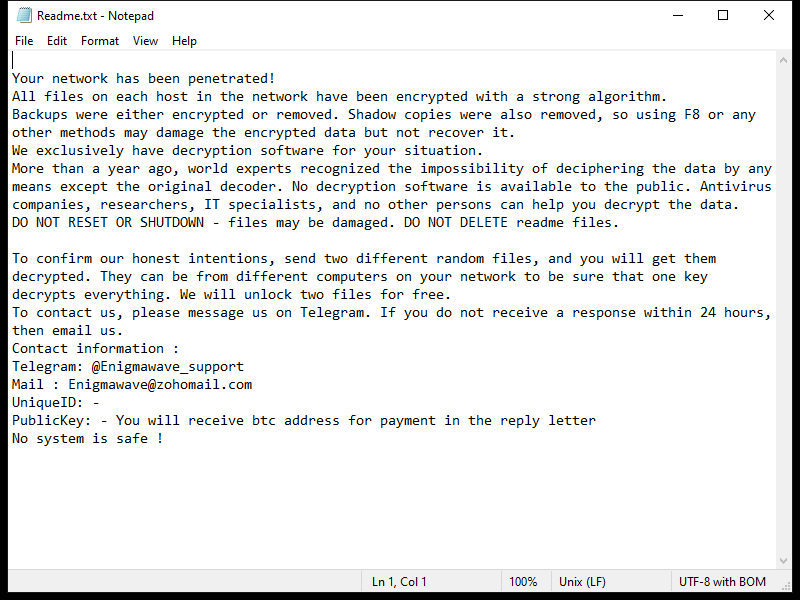
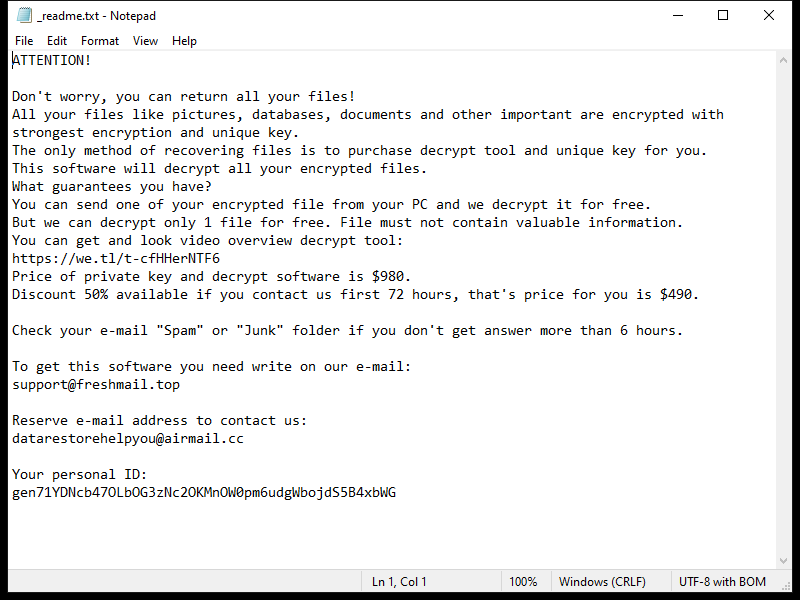
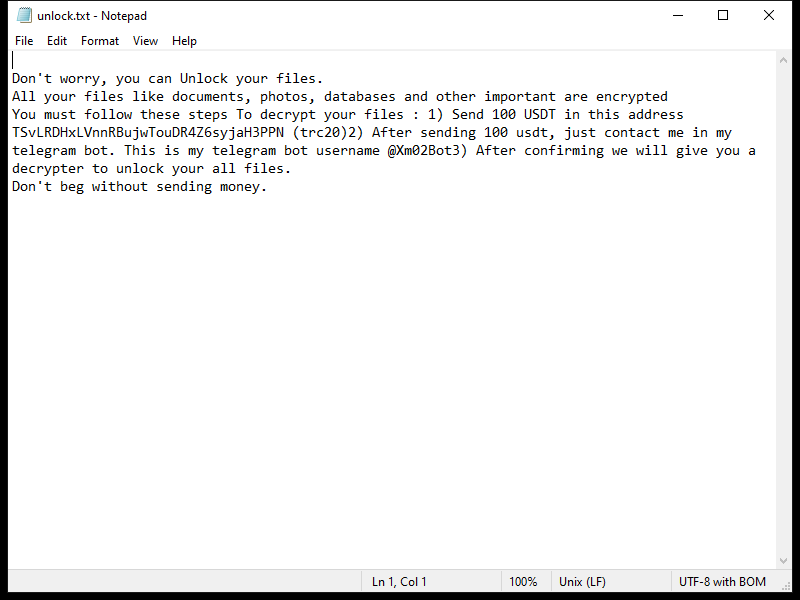
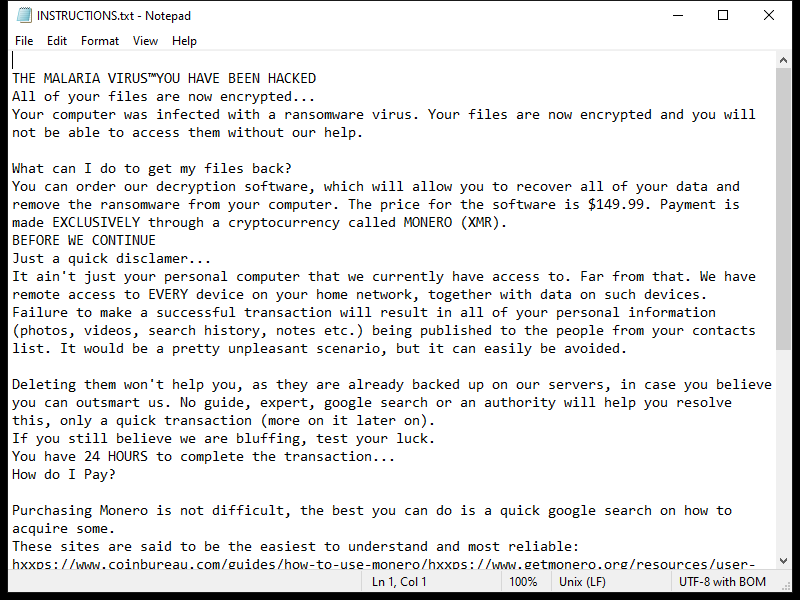
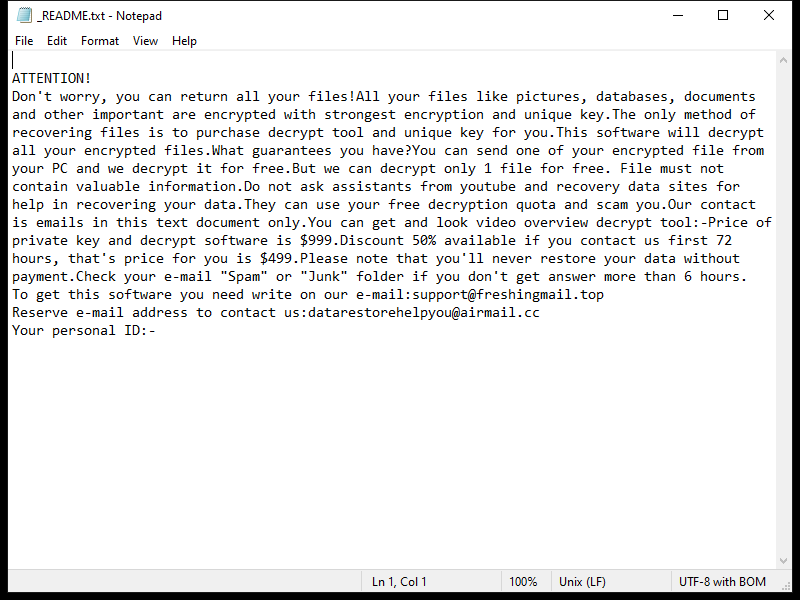
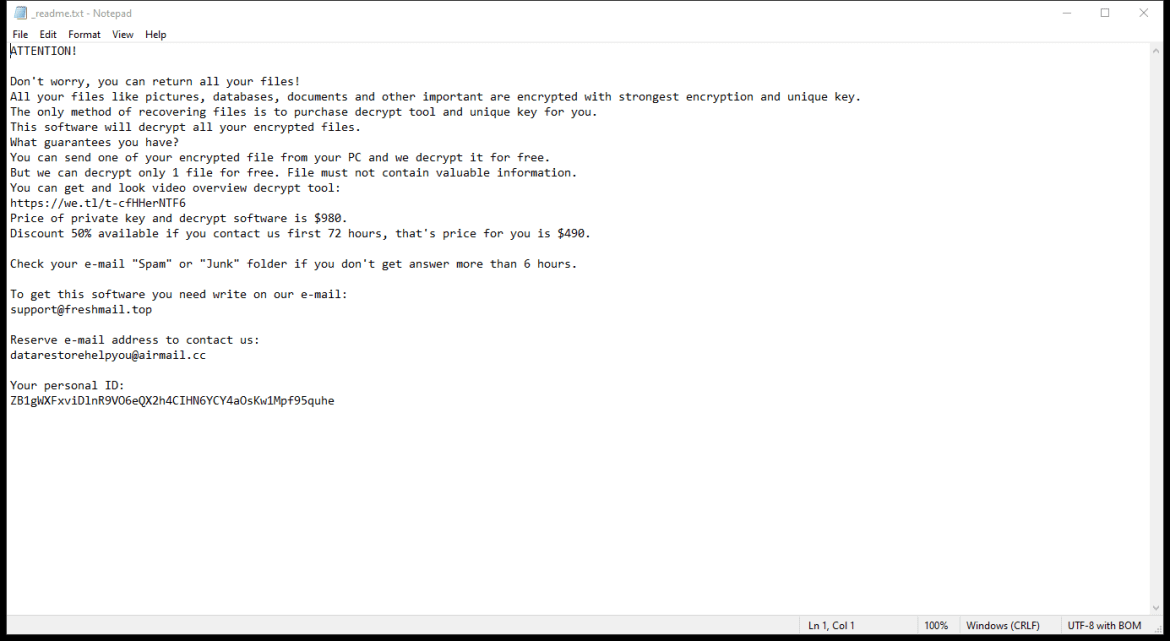
After encrypting files, Capibara Ransomware creates a ransom note on the desktop or in folders containing encrypted files. The ransom note usually contains instructions on how to pay the ransom to get the decryption key.
As of now, there are no known decryption tools available for Capibara Ransomware. However, it is not recommended to pay the ransom as there is no guarantee that the cybercriminals will provide the decryption key or that it will work effectively.
To decrypt .capibara files, you can try restoring files from a backup, using file recovery software, or seeking help from cybersecurity professionals. It is important to regularly back up your files to prevent data loss in case of a ransomware attack.