What is Trojan:Win32/Vundo!Av and how it infects computers
Trojan:Win32/Vundo!Av is a type of Trojan horse malware that primarily targets computers running on the Windows operating system. It is known to be a variant of the Vundo Trojan, which has been prevalent since 2007. Trojan:Win32/Vundo!Av is designed to perform malicious activities on the infected system, such as stealing sensitive information, downloading additional malware, and displaying unwanted advertisements.
There are several ways through which Trojan:Win32/Vundo!Av can infect computers:
1. Exploiting Software Vulnerabilities: The Trojan can take advantage of security vulnerabilities in software applications or the operating system to gain unauthorized access to the system.
2. Drive-by Downloads: It can be downloaded onto a user’s computer unknowingly when visiting compromised or malicious websites. These websites may exploit security vulnerabilities in the user’s browser or use social engineering techniques to trick the user into downloading and executing the Trojan.
3. Malicious Email Attachments: The Trojan can be distributed through spam emails that contain infected attachments. When the user opens the attachment, the Trojan gets executed, infecting the computer.
4. Peer-to-peer (P2P) File Sharing: Trojan:Win32/Vundo!Av can also spread through file-sharing networks, where infected files are shared among users. When a user downloads and executes an infected file, the Trojan infects their system.
Once installed, Trojan:Win32/Vundo!Av can modify system settings, inject malicious code into legitimate processes, and create registry entries to ensure its persistence on the infected system. It may also disable security software to avoid detection and removal.
To protect your computer from Trojan:Win32/Vundo!Av and other malware, it is essential to keep your operating system and applications up to date, use reliable antivirus software, exercise caution when opening email attachments or downloading files from the internet, and avoid visiting suspicious or malicious websites.
Download Trojan:Win32/Vundo!Av Removal Tool
SpyHunter 5 is a powerful malware detection and removal tool developed by EnigmaSoft Limited. It’s designed to provide robust protection against a wide range of malware threats, including viruses, trojans, worms, rootkits, and ransomware. SpyHunter 5 is particularly known for its effectiveness in dealing with complex and evolving malware types that traditional antivirus programs may struggle to detect.
Manual removal of Trojan:Win32/Vundo!Av
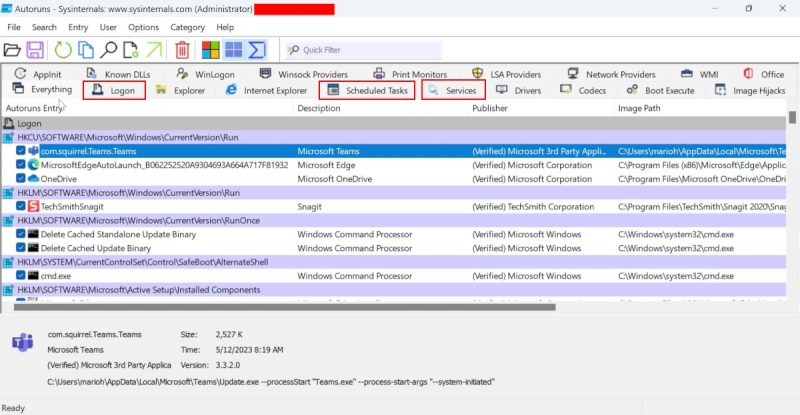
Use Autoruns to detect and remove malicious processes and services, related to Trojan:Win32/Vundo!Av
Using Autoruns to detect potential viruses involves several steps. Autoruns is a utility from Microsoft that shows you which programs are configured to run during system bootup or login. Here’s a detailed guide:
- Download and Install Autoruns:
Visit the Microsoft Sysinternals website and download the latest version of Autoruns.
Extract the downloaded ZIP file to a folder of your choice. - Run Autoruns:
Right-click the Autoruns.exe file and choose Run as administrator to ensure it has the necessary permissions.
Autoruns needs a few moments to gather information about the programs that start on your system. - Filter legitimate entries:
In the Autoruns, click Options at the top menu and uncheck Hide Empty Locations and check Hide Windows Entries options. After this procedure, click the Refresh icon.
- Analyze the Results:
Once Autoruns has finished loading, you’ll see a list of all the programs and services that start with Windows.
Important tabs include Logon, Services, and Scheduled Tasks. - Identify Suspicious Entries:
Look for entries with File not found status or those with no publisher information. These can be red flags.
Be cautious of entries with unusual file paths or names. - Research Unknown Entries:
If you find an entry that you’re unsure about, research it online. A quick web search of the name can often provide clarity on whether it’s legitimate or potentially harmful.
- Disable or Delete Suspicious Entries:
To prevent an item from running, simply uncheck the box next to it. This doesn’t delete the program, but stops it from running at startup.
If you’re confident an entry is malicious, you can right-click and delete it. Be very careful with this option, as deleting system files can harm your PC. - Reboot and Monitor Your PC:
After making changes, reboot your computer.
Monitor your system’s performance and behavior. If something doesn’t work correctly, you may need to re-enable an item you disabled. - Regular Checks:
It’s a good idea to use Autoruns periodically to check for any new or unusual entries.
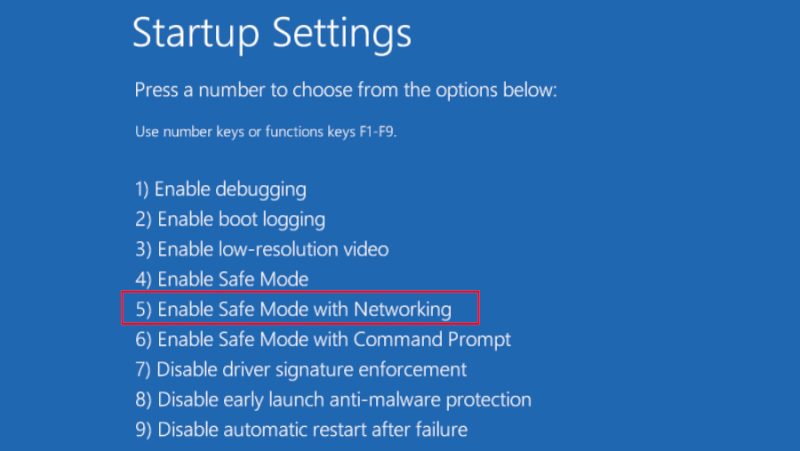
Load in Safe Mode with Networking
Loading Windows 10 or Windows 11 in Safe Mode with Networking is a straightforward process, although it slightly differs between the two versions. Safe Mode with Networking starts Windows in a basic state, using a limited set of files and drivers but includes those necessary for networking. This mode can help troubleshoot and diagnose issues with your PC.
For Windows 10:
From the Sign-In Screen:
- Restart your PC. When you reach the sign-in screen, hold the Shift key down while you select Power > Restart.
- After your PC restarts, go to the Choose an option screen, select Troubleshoot > Advanced options > Startup Settings > Restart.
- Once your PC restarts again, a list of options will appear. Choose 5 or F5 to start your PC in Safe Mode with Networking.
From Settings:
- Open Settings > Update & Security > Recovery.
- Under Advanced startup, select Restart now.
- After your PC restarts to the Choose an option screen, select Troubleshoot > Advanced options > Startup Settings > Restart.
- After your PC restarts, select 5 or F5 for Safe Mode with Networking.
For Windows 11:
From the Sign-In Screen:
- Restart your PC. At the sign-in screen, select the Power icon, hold the Shift key, and choose Restart.
- After your PC restarts, you will see the Choose an option screen. Navigate to Troubleshoot > Advanced options > Startup Settings and click Restart.
- When it restarts again, a list of options will appear. Press 5 or F5 to boot into Safe Mode with Networking.
From Settings:
- Open Settings > System > Recovery.
- Under Recovery options, next to Advanced startup, click Restart now.
- After the PC restarts to the Choose an option screen, go to Troubleshoot > Advanced options > Startup Settings and then click Restart.
- Once it restarts, press 5 or F5 to choose Safe Mode with Networking.
In both Windows 10 and Windows 11, Safe Mode with Networking allows you to access the internet and use network drivers, which can be useful for downloading drivers, updates, or running online troubleshooting tools. Remember that in Safe Mode, your PC’s functionality will be limited.
Use Microsoft Windows Malicious Software Removal Tool (MSRT) to remove Trojan:Win32/Vundo!Av
The Microsoft Windows Malicious Software Removal Tool (MSRT) is a useful utility that checks for and removes prevalent malware from Windows computers. Here’s how you can use it in Windows 10 and Windows 11:
- Download the Tool:
MSRT is typically delivered through Windows Update, so it’s likely already installed on your system. If you want to run the latest version, you can download it directly from Microsoft’s website.
Go to the Microsoft website and search for the “Malicious Software Removal Tool”, then download the version appropriate for your system (32-bit or 64-bit). - Run the Tool:
Once downloaded, locate the file (usually named mrt.exe) and double-click it to run.
If you’re using Windows 10, you can also find it by typingmrtinto the search box near the Start menu, then selecting it from the search results.
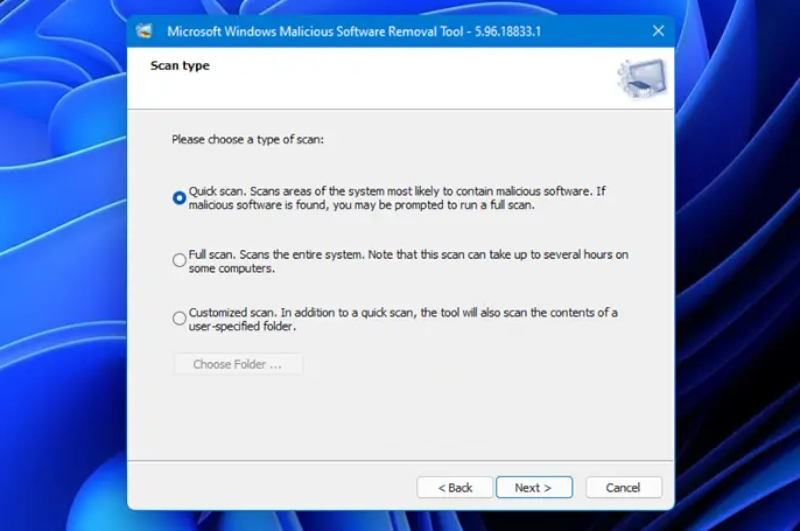
In Windows 11, press Windows key + S to open the search bar, type mrt, and click on the tool when it appears. - Using the Tool:
When you start the MSRT, it will first show a welcome screen and license terms. Click Next to proceed.
You’ll then have the option to choose the type of scan:
Quick scan: Scans areas of the system most likely to contain malware. This is the fastest option.
Full scan: Scans the entire system. It’s thorough but can take a long time, especially on large or full drives.
Customized scan: Allows you to choose specific folders to scan. - Run the Scan:
Select the type of scan you prefer and click Next. The scan will begin.
Depending on the scan type and the size of your hard drive, the process can take several minutes to a few hours. - Review and Remove Malware:
After the scan completes, MSRT will report any detected malware and offer to remove it.
Follow the prompts to remove any detected malware. The tool will give you a report of what was found and removed. - Close the Tool:
Once the removal process is complete, click Finish to close the tool.
- Check the Detailed Log File (Optional):
If you want more detailed information about the scan, MSRT creates a log file in
Windows\Debug named mrt.log.
Remember, while MSRT can remove many prevalent types of malware, it’s not a replacement for an antivirus program. It’s designed to complement regular antivirus software, not substitute it. Therefore, ensure you have a robust antivirus solution for ongoing protection against a broader range of threats.
How to prevent Trojan:Win32/Vundo!Av infection?
It is always rewarding to prevent virus infection because of the consequences it may bring. There are a lot of difficulties in resolving issues with encoders viruses, that’s why it is very vital to keep a proper and reliable anti-malware software on your computer. In case you don’t have any, here you may find some of the best offers in order to protect your PC from disastrous viruses.
SpyHunter is a reliable antimalware removal tool application, that is able to protect your PC and prevent the infection from the start. The program is designed to be user-friendly and multi-functional.