What is QRYPT Ransomware
QRYPT Ransomware is a type of malware that encrypts files on a computer and demands a ransom for the decryption key. It typically infects computers through malicious email attachments, exploit kits, or by exploiting vulnerabilities in software.
Once a computer is infected, QRYPT Ransomware will encrypt files on the system and add the “.qcrypt” extension to them. It uses strong encryption algorithms like AES or RSA to encrypt the files, making them inaccessible without the decryption key.
After encrypting the files, QRYPT Ransomware will create a ransom note typically named “README_QRYPT.txt” or similar, which contains instructions on how to pay the ransom in exchange for the decryption key. The ransom note is usually placed in folders containing encrypted files or on the desktop.
As of now, there are no decryption tools available for QRYPT Ransomware. However, it is not recommended to pay the ransom as there is no guarantee that the cybercriminals will provide the decryption key.
If your files have been encrypted by QRYPT Ransomware, you can try to restore them from backups if you have them. You can also try using data recovery software to recover some of the files. Additionally, you can seek help from cybersecurity professionals or law enforcement agencies for further assistance.
You can not trust scammers and pay money without a guarantee of receiving files. The most effective way to get your files back is to remove QRYPT Ransomware to prevent infection. There are 2 options for solving this problem. The first is to use an automatic removal utility that will remove the threat and all instances related to it. Moreover, it will save you time. Or you can use the Manual Removal Guide, but you should know that it might be very difficult to remove QRYPT Ransomware manually without a specialist’s help. If for any reason you need to recover deleted or lost files, then check out our article Top 5 Deleted File Recovery Software
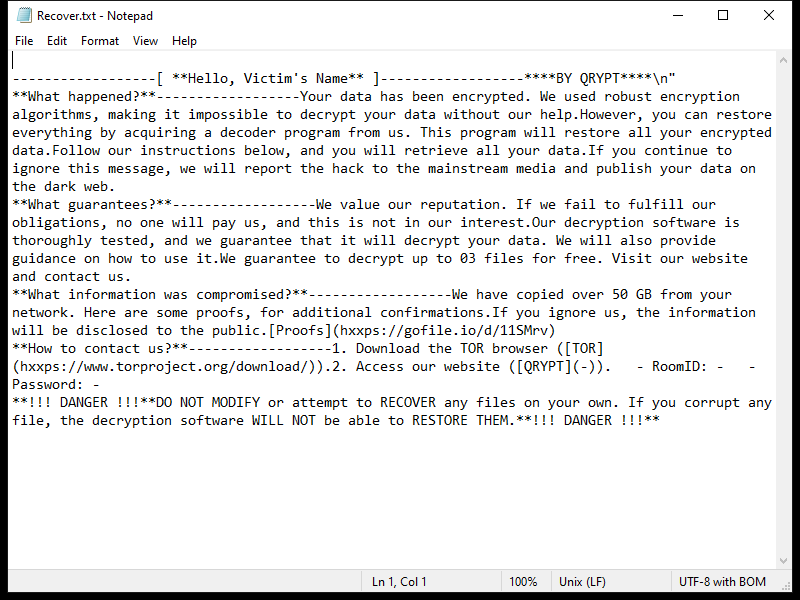
Contents of the ransom note:
------------------[ **Hello, Victim's Name** ]------------------****BY QRYPT****\n"
**What happened?**------------------Your data has been encrypted. We used robust encryption algorithms, making it impossible to decrypt your data without our help.However, you can restore everything by acquiring a decoder program from us. This program will restore all your encrypted data.Follow our instructions below, and you will retrieve all your data.If you continue to ignore this message, we will report the hack to the mainstream media and publish your data on the dark web.
**What guarantees?**------------------We value our reputation. If we fail to fulfill our obligations, no one will pay us, and this is not in our interest.Our decryption software is thoroughly tested, and we guarantee that it will decrypt your data. We will also provide guidance on how to use it.We guarantee to decrypt up to 03 files for free. Visit our website and contact us.
**What information was compromised?**------------------We have copied over 50 GB from your network. Here are some proofs, for additional confirmations.If you ignore us, the information will be disclosed to the public.[Proofs](hxxps://gofile.io/d/11SMrv)
**How to contact us?**------------------1. Download the TOR browser ([TOR](hxxps://www.torproject.org/download/)).2. Access our website ([QRYPT](-)). - RoomID: - - Password: -
**!!! DANGER !!!**DO NOT MODIFY or attempt to RECOVER any files on your own. If you corrupt any file, the decryption software WILL NOT be able to RESTORE THEM.**!!! DANGER !!!**
QRYPT Ransomware Removal Guide

Remember that you need to remove QRYPT Ransomware first and foremost to prevent further encryption of your files before the state of your data becomes totally useless. And only after that, you can start recovering your files. Removal must be performed according to the following steps:
Download QRYPT Ransomware Removal Tool
SpyHunter 5 is a powerful malware detection and removal tool developed by EnigmaSoft Limited. It’s designed to provide robust protection against a wide range of malware threats, including viruses, trojans, worms, rootkits, and ransomware. SpyHunter 5 is particularly known for its effectiveness in dealing with complex and evolving malware types that traditional antivirus programs may struggle to detect.
Manual QRYPT Ransomware Removal Guide
Here are step-by-step instructions to remove QRYPT Ransomware from Windows. Follow these steps carefully and remove files and folders belonging to QRYPT Ransomware. Firstly, you need to run the system in a Safe Mode. Then find and remove needed files and folders.
QRYPT Ransomware files:
{randomname}.exe, Recover.txt
Clean up hosts file to access security websites
Cleaning up the “hosts” file from unwanted entries involves a few steps. The “hosts” file is a system file used by an operating system to map hostnames to IP addresses. Often, viruses add entries to block popular antivirus websites. It’s important to be cautious when editing this file, as incorrect modifications can cause network issues. Here’s a general guide on how to clean it up:
- Open Notepad as an Administrator:
- Type ‘Notepad’ in the search bar.
- Right-click on the Notepad app and select ‘Run as administrator’.
- Open the Hosts File in Notepad:
- In Notepad, go to File > Open.
- Navigate to
C:\Windows\System32\drivers\etc. - Select “All Files” from the drop-down menu next to the filename text box.
- Open the “hosts” file.
- Edit the File:
- Locate any unwanted entries. These are typically at the bottom of the file.
- Remove or comment them out by adding a
#at the beginning of the line.
- Save Your Changes:
- Go to File > Save.
- Close Notepad.
Check for malicious processes on Windows
Checking for malicious processes in Windows involves a few steps and the use of some tools. While some basic checks can be done manually, for a more thorough examination, specialized software is often required. Here’s a guide to help you get started:
- Task Manager:
- Press
Ctrl + Shift + Escto open Task Manager. - Go to the Processes tab.
- Look for any unusual or unfamiliar processes, especially those using high CPU or memory.
- Right-click on a suspicious process and select Open file location to investigate further.
- Press
- Resource Monitor:
- Access Resource Monitor by typing Resource Monitor in the Start menu search bar.
- Check the Overview or CPU tab for suspicious activities.
Remove unwanted startup entries
- Open System Configuration:
- Press
Windows Key + Rto open the Run dialog box. - Type
msconfigand press Enter. This opens the System Configuration window.
- Press
- Navigate to the Startup Tab:
- In the System Configuration window, go to the Startup tab.
- Note: In Windows 10 and later, you might be redirected to the Task Manager for managing startup items.
- Disable Unwanted Startup Programs:
- If within System Configuration, uncheck the boxes next to the programs you want to disable.
- If in Task Manager, select the program and click Disable.
- Apply Changes and Restart:
- Click OK or Apply to save your changes.
- Restart your computer if prompted.
How to decrypt .qcrypt files
You can try to restore your files with special tools. You may find more detailed info on data recovery software in this article – recovery software. These programs may help you to restore files that were infected and encrypted by ransomware.
Restore data with Stellar Data Recovery
Stellar Data Recovery is able to find and restore different types of encrypted files, including removed emails.
- Download and install Stellar Data Recovery
- Choose drives and folders with your data, then press Scan.
- Select all the files in a folder, then click on Restore button.
- Manage export location. That’s it!
Restore data with Aiseesoft Data Recovery
Aiseesoft Data Recovery recovers deleted files (like photos, documents, emails, audio, video), and also recovers from a computer, hard drive, flash drive, memory card, digital cameras. Recover from accidental deletion, formatted partition, hard drive problem, RAW hard drive, computer crash. We hope this guide was helpful to you. Feel free to leave a comment and tell us what recovery software was (or wasn’t) effective in your case.
Use Windows Previous Versions or Shadow Explorer to recover .qcrypt files
Using Windows Previous Versions and Shadow Explorer to restore files is a valuable technique, especially when dealing with accidental deletions or file corruptions. It can also be helpful in case of ransomware infections. Here’s how to use each feature:
Using Windows Previous Versions
- Find the File or Folder:
- Right-click on the file or folder you want to restore.
- Select Properties from the context menu.
- Access Previous Versions:
- In the Properties dialog, go to the Previous Versions tab.
- You’ll see a list of available previous versions from restore points or File History backups.
- Restore the File or Folder:
- Select the version you want to restore.
- Click Restore to overwrite the current version, or Copy to place it in a different location.
Using Shadow Explorer
- Download and Install Shadow Explorer:
- Download Shadow Explorer from its official website.
- Install and open the application.
- Select the Volume and Date:
- At the top of the Shadow Explorer window, select the desired drive (volume).
- Choose the date of the shadow copy you want to explore.
- Navigate and Restore Files:
- Navigate through the file system as in Windows Explorer.
- Right-click on the file or folder you wish to restore.
- Select Export and choose where to save the restored file.
How to prevent ransomware infection?
It is always rewarding to prevent ransomware infection because of the consequences it may bring. There are a lot of difficulties in resolving issues with encoders viruses, that’s why it is very vital to keep a proper and reliable anti-ransomware software on your computer. In case you don’t have any, here you may find some of the best offers in order to protect your PC from disastrous viruses.
SpyHunter is a reliable antimalware removal tool application, that is able to protect your PC and prevent the infection from the start. The program is designed to be user-friendly and multi-functional.
