What is Z1n Ransomware
Z1n Ransomware is a type of malicious software that infects computers and encrypts files, making them inaccessible to the user. Here is some information about Z1n Ransomware:
1. Infection: Z1n Ransomware typically infects computers through various methods, including phishing emails, malicious attachments, fake software updates, or exploiting vulnerabilities in outdated software.
2. File Extensions: Z1n Ransomware adds the “.z1n” extension to encrypted files. For example, a file named “document.doc” will be renamed as “document.doc.z1n” after encryption.
3. File Encryption: Z1n Ransomware uses strong encryption algorithms like AES or RSA to encrypt the victim’s files. This encryption makes the files unreadable without the decryption key.
4. Ransom Note: Z1n Ransomware usually creates a ransom note in the form of a text file or a pop-up message. The note contains instructions on how to pay the ransom to obtain the decryption key. The location and name of the ransom note may vary, but it is often placed on the user’s desktop or within folders containing encrypted files.
5. Decryption Tools: At the time of writing, there are no known decryption tools available for Z1n Ransomware. It is always recommended to avoid paying the ransom, as it does not guarantee the recovery of your files, supports criminal activities, and encourages further development of ransomware.
6. Decrypting .z1n Files: Since no decryption tools are available, restoring files encrypted by Z1n Ransomware can be challenging. However, you may try the following steps:
a. Remove the ransomware: Use an up-to-date antivirus program to scan and remove the Z1n Ransomware from your computer.
b. Restore from backup: If you have a recent backup of your files, you can restore them after ensuring that the ransomware is completely removed from your system.
c. Consult professionals: In some cases, data recovery professionals may be able to decrypt your files or provide alternative solutions. However, this can be costly and may not guarantee success.
Remember, prevention is key to avoid ransomware infections. Regularly update your operating system and software, use reliable antivirus software, avoid opening suspicious emails or downloading files from untrusted sources, and maintain secure backups of your important files.
You can not trust scammers and pay money without a guarantee of receiving files. The most effective way to get your files back is to remove Z1n Ransomware to prevent infection. There are 2 options for solving this problem. The first is to use an automatic removal utility that will remove the threat and all instances related to it. Moreover, it will save you time. Or you can use the Manual Removal Guide, but you should know that it might be very difficult to remove Z1n Ransomware manually without a specialist’s help. If for any reason you need to recover deleted or lost files, then check out our article Top 5 Deleted File Recovery Software
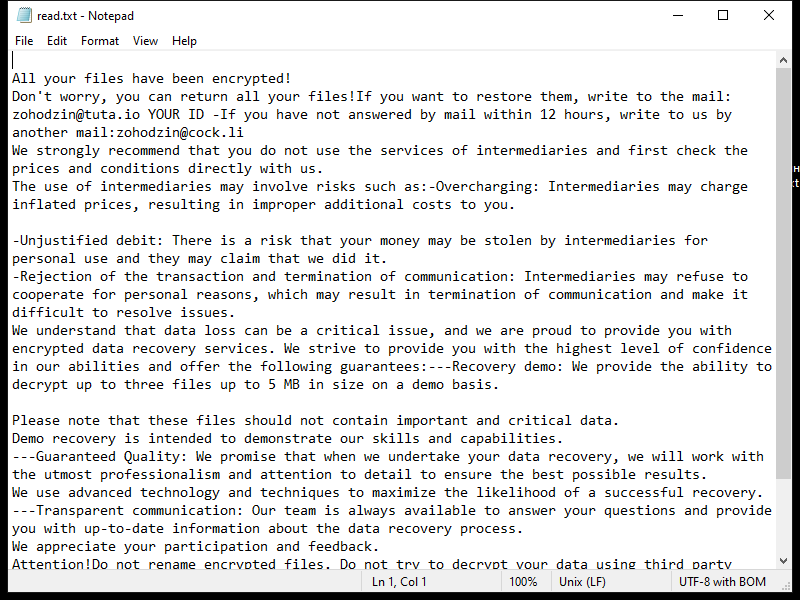
Contents of the ransom note:
All your files have been encrypted!
Don't worry, you can return all your files!If you want to restore them, write to the mail: zohodzin@tuta.io YOUR ID -If you have not answered by mail within 12 hours, write to us by another mail:zohodzin@cock.li
We strongly recommend that you do not use the services of intermediaries and first check the prices and conditions directly with us.
The use of intermediaries may involve risks such as:-Overcharging: Intermediaries may charge inflated prices, resulting in improper additional costs to you.
-Unjustified debit: There is a risk that your money may be stolen by intermediaries for personal use and they may claim that we did it.
-Rejection of the transaction and termination of communication: Intermediaries may refuse to cooperate for personal reasons, which may result in termination of communication and make it difficult to resolve issues.
We understand that data loss can be a critical issue, and we are proud to provide you with encrypted data recovery services. We strive to provide you with the highest level of confidence in our abilities and offer the following guarantees:---Recovery demo: We provide the ability to decrypt up to three files up to 5 MB in size on a demo basis.
Please note that these files should not contain important and critical data.
Demo recovery is intended to demonstrate our skills and capabilities.
---Guaranteed Quality: We promise that when we undertake your data recovery, we will work with the utmost professionalism and attention to detail to ensure the best possible results.
We use advanced technology and techniques to maximize the likelihood of a successful recovery.
---Transparent communication: Our team is always available to answer your questions and provide you with up-to-date information about the data recovery process.
We appreciate your participation and feedback.
Attention!Do not rename encrypted files. Do not try to decrypt your data using third party software, it may cause permanent data loss. Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Z1n Ransomware Removal Guide

Remember that you need to remove Z1n Ransomware first and foremost to prevent further encryption of your files before the state of your data becomes totally useless. And only after that, you can start recovering your files. Removal must be performed according to the following steps:
Download Z1n Ransomware Removal Tool
SpyHunter 5 is a powerful malware detection and removal tool developed by EnigmaSoft Limited. It’s designed to provide robust protection against a wide range of malware threats, including viruses, trojans, worms, rootkits, and ransomware. SpyHunter 5 is particularly known for its effectiveness in dealing with complex and evolving malware types that traditional antivirus programs may struggle to detect.
Manual Z1n Ransomware Removal Guide
Here are step-by-step instructions to remove Z1n Ransomware from Windows. Follow these steps carefully and remove files and folders belonging to Z1n Ransomware. Firstly, you need to run the system in a Safe Mode. Then find and remove needed files and folders.
Z1n Ransomware files:
{randomname}.exe, read.txt
Clean up hosts file to access security websites
Cleaning up the “hosts” file from unwanted entries involves a few steps. The “hosts” file is a system file used by an operating system to map hostnames to IP addresses. Often, viruses add entries to block popular antivirus websites. It’s important to be cautious when editing this file, as incorrect modifications can cause network issues. Here’s a general guide on how to clean it up:
- Open Notepad as an Administrator:
- Type ‘Notepad’ in the search bar.
- Right-click on the Notepad app and select ‘Run as administrator’.
- Open the Hosts File in Notepad:
- In Notepad, go to File > Open.
- Navigate to
C:\Windows\System32\drivers\etc. - Select “All Files” from the drop-down menu next to the filename text box.
- Open the “hosts” file.
- Edit the File:
- Locate any unwanted entries. These are typically at the bottom of the file.
- Remove or comment them out by adding a
#at the beginning of the line.
- Save Your Changes:
- Go to File > Save.
- Close Notepad.
Check for malicious processes on Windows
Checking for malicious processes in Windows involves a few steps and the use of some tools. While some basic checks can be done manually, for a more thorough examination, specialized software is often required. Here’s a guide to help you get started:
- Task Manager:
- Press
Ctrl + Shift + Escto open Task Manager. - Go to the Processes tab.
- Look for any unusual or unfamiliar processes, especially those using high CPU or memory.
- Right-click on a suspicious process and select Open file location to investigate further.
- Press
- Resource Monitor:
- Access Resource Monitor by typing Resource Monitor in the Start menu search bar.
- Check the Overview or CPU tab for suspicious activities.
Remove unwanted startup entries
- Open System Configuration:
- Press
Windows Key + Rto open the Run dialog box. - Type
msconfigand press Enter. This opens the System Configuration window.
- Press
- Navigate to the Startup Tab:
- In the System Configuration window, go to the Startup tab.
- Note: In Windows 10 and later, you might be redirected to the Task Manager for managing startup items.
- Disable Unwanted Startup Programs:
- If within System Configuration, uncheck the boxes next to the programs you want to disable.
- If in Task Manager, select the program and click Disable.
- Apply Changes and Restart:
- Click OK or Apply to save your changes.
- Restart your computer if prompted.
How to decrypt .z1n files
You can try to restore your files with special tools. You may find more detailed info on data recovery software in this article – recovery software. These programs may help you to restore files that were infected and encrypted by ransomware.
Restore data with Stellar Data Recovery
Stellar Data Recovery is able to find and restore different types of encrypted files, including removed emails.
- Download and install Stellar Data Recovery
- Choose drives and folders with your data, then press Scan.
- Select all the files in a folder, then click on Restore button.
- Manage export location. That’s it!
Restore data with Aiseesoft Data Recovery
Aiseesoft Data Recovery recovers deleted files (like photos, documents, emails, audio, video), and also recovers from a computer, hard drive, flash drive, memory card, digital cameras. Recover from accidental deletion, formatted partition, hard drive problem, RAW hard drive, computer crash. We hope this guide was helpful to you. Feel free to leave a comment and tell us what recovery software was (or wasn’t) effective in your case.
Use Windows Previous Versions or Shadow Explorer to recover .z1n files
Using Windows Previous Versions and Shadow Explorer to restore files is a valuable technique, especially when dealing with accidental deletions or file corruptions. It can also be helpful in case of ransomware infections. Here’s how to use each feature:
Using Windows Previous Versions
- Find the File or Folder:
- Right-click on the file or folder you want to restore.
- Select Properties from the context menu.
- Access Previous Versions:
- In the Properties dialog, go to the Previous Versions tab.
- You’ll see a list of available previous versions from restore points or File History backups.
- Restore the File or Folder:
- Select the version you want to restore.
- Click Restore to overwrite the current version, or Copy to place it in a different location.
Using Shadow Explorer
- Download and Install Shadow Explorer:
- Download Shadow Explorer from its official website.
- Install and open the application.
- Select the Volume and Date:
- At the top of the Shadow Explorer window, select the desired drive (volume).
- Choose the date of the shadow copy you want to explore.
- Navigate and Restore Files:
- Navigate through the file system as in Windows Explorer.
- Right-click on the file or folder you wish to restore.
- Select Export and choose where to save the restored file.
How to prevent ransomware infection?
It is always rewarding to prevent ransomware infection because of the consequences it may bring. There are a lot of difficulties in resolving issues with encoders viruses, that’s why it is very vital to keep a proper and reliable anti-ransomware software on your computer. In case you don’t have any, here you may find some of the best offers in order to protect your PC from disastrous viruses.
SpyHunter is a reliable antimalware removal tool application, that is able to protect your PC and prevent the infection from the start. The program is designed to be user-friendly and multi-functional.
